Business
How to Conduct a Comprehensive Security Audit for Your Business Premises

Most business owners believe that a security audit involves verifying that the doors are closed and the cameras are functioning. That isn’t an audit – it’s a walkthrough. An audit would treat your premises as three concentric rings: the perimeter, the shell, and the high-value zones. Each ring must be assessed on its own merits because a weakness in one doesn’t counteract the strength of another. It just means an intruder goes further before they’re stopped.
Take the fence line. Are gates closing properly, bollards not moved by delivery trucks, and perimeter lighting not shining right across access points the CCTV is supposed to be monitoring? Then go inward. The building shell is every door, every window, and every service hatch – not just the front door. Internal zones are your server room, the cash office, and any room a contractor shouldn’t be allowed to roam in unaccompanied.
Run through all three rings before making any judgements. You’ll often discover a business has tight internal controls and almost no perimeter discipline, meaning the investment in the inner ring was largely wasted.
Do The Night Walk
Checking the lighting under daylight conditions comes off as a half-measure. Come a couple hours after nightfall, to do a proper walkthrough. The best practice is to bring two representatives on your tour: one to walk around the exterior, checking lights and alternate points of entry, and one to watch your real-time feed from one of your internal cameras showing their approach to the door.
The litmus test of effective lighting is really pretty simple. You ought to be able to see the other person’s face clearly over that camera. If you can’t, you’re just throwing good money after bad on video surveillance that’s not usable for prosecution or insurance purposes.
The Human Element Is Where Most Audits Stop Short
Access control systems are only as good as the logs of who is actually going where, when. So, ask for the last thirty days of entry data from yours right now. That’s enough for you to look out for patterns: doors held open to ease delivery, the same keycard unlocking the door to your server room when you’re closed for business, or badge-ins that don’t match against your shift records.
Tailgating, or following someone with a legitimate cause to open the door and making your way in without badging yourself, is one of the most common and most underestimated ways commercial premises get burgled. You can’t solve it with technology but a mantrap vestibule – basically an airlock-style entry with two interlocking, automatically-sealing doors – does the job just fine. So does a sign telling guests, contractors, and staff that they must badge, and the guard’s mobile number to check identities. Internal theft also deserves the audit treatment.
Your insurance company won’t always be pleased if what they’ve come to recover is already missing, but access logs, inventory discrepancies, and contractor movement records speak louder than a week’s worth of camera footage.
Hardware And Software Need To Be Audited Together
This is the section where most self-audits drop the ball completely. All your physical security hardware – your smart locks, your alarm panels, your intercom systems – they all run on firmware. That firmware has security vulnerabilities, and the vendors push out updated versions to close them. An out-of-date lock that is part of your network is an IT security problem, not a physical one.
Similarly, an alarm system that only connects to a local siren is a neighborhood security feature. A properly monitored alarm system connects to a 24/7 professional monitoring center and is what’s known as a “force multiplier”: one of ten things that make your physical neighborhood 10 times less likely to be robbed. The difference in operation between the two is immense.
For businesses moving from a do-it-yourself audit to a do-it-for-real procurement process, a security company Adelaide that can easily deal with both the hardware and the monitoring side means that the results of your security audit become a plan, not a shopping list.
Backup batteries on alarm panels, camera lenses that haven’t been cleaned in two years, sensors with weak signals – these are maintenance issues, not upgrade issues. A security audit that doesn’t include a maintenance check is missing the section that shows the largest number of system failures.
Turn Findings Into A Living Document
A finalized audit should result in a risk assessment matrix that evaluates each discovery based on the likelihood of it occurring and the potential impact if it did. While you won’t be able to remediate every weakness right away, you should be able to set a deadline and assign responsibility for all of them.
Fire safety is a good example of this step. Blocking fire doors or failing to provide or communicate evacuation routes are both immediate and potentially disastrous issues. Sadly, they pop up in audit findings far too often. If the auditor identifies a problem that could put lives at risk, the clock starts ticking right then and there. Fix it or lose your certification. There isn’t a clearer, more direct instruction out there.
You should update this report every six months at the outside. Your team changes, your footprint changes, and the threat environment changes. This should not be an annual scavenger hunt. Yet, at some organizations, it is. Then they wonder how they could have missed the writing on the wall about a breach when it was right there in last year’s report.
This update should be an honest picture of your situation: this is everything that has changed since the last report. It also creates a gameplan for the next six months.
-

 Celebrity1 year ago
Celebrity1 year agoWho Is Jennifer Rauchet?: All You Need To Know About Pete Hegseth’s Wife
-

 Celebrity1 year ago
Celebrity1 year agoWho Is Mindy Jennings?: All You Need To Know About Ken Jennings Wife
-
 Celebrity1 year ago
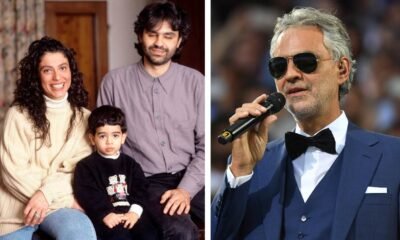
Celebrity1 year agoWho Is Enrica Cenzatti?: The Untold Story of Andrea Bocelli’s Ex-Wife
-

 Celebrity2 years ago
Celebrity2 years agoWho Is Klarissa Munz: The Untold Story of Freddie Highmore’s Wife
















